Preparing on-premises and AWS environments for external Kerberos authentication for Amazon RDS | AWS Database Blog
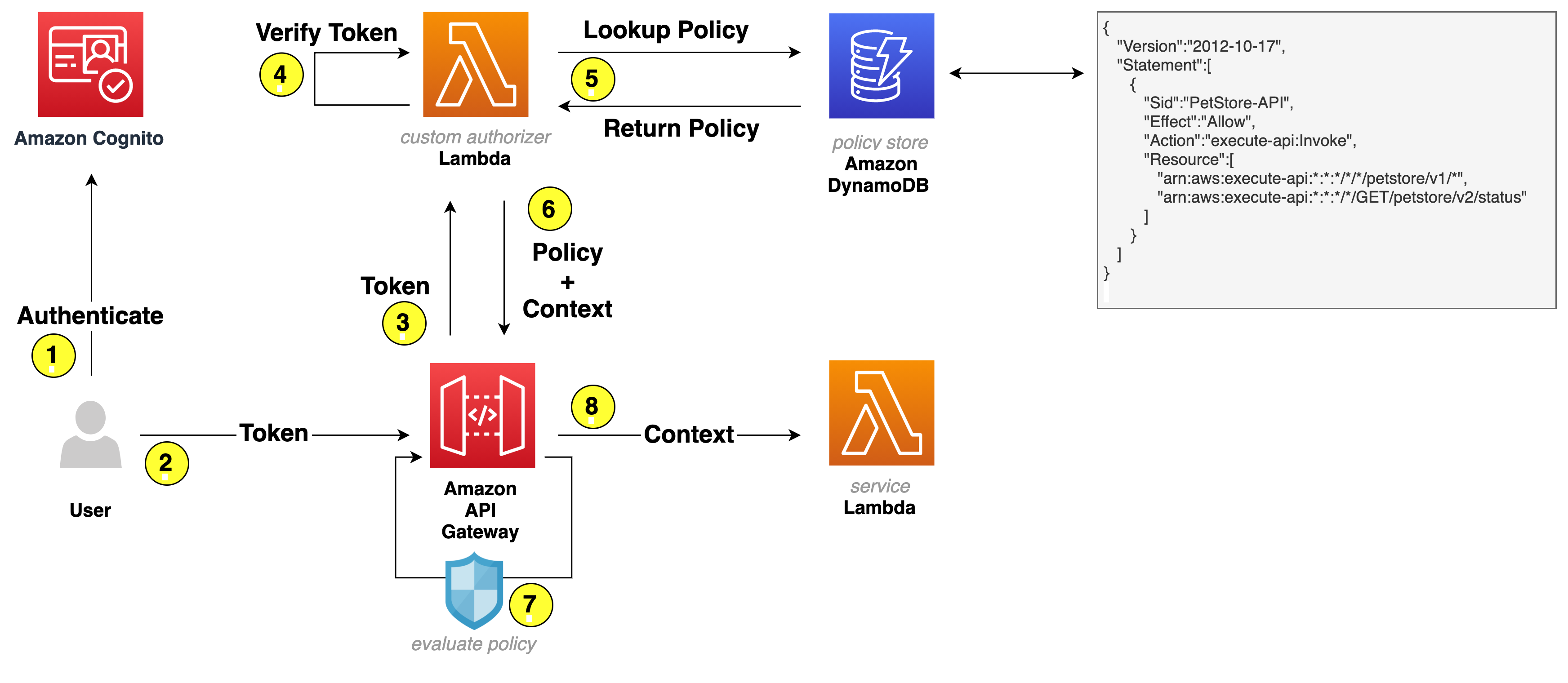
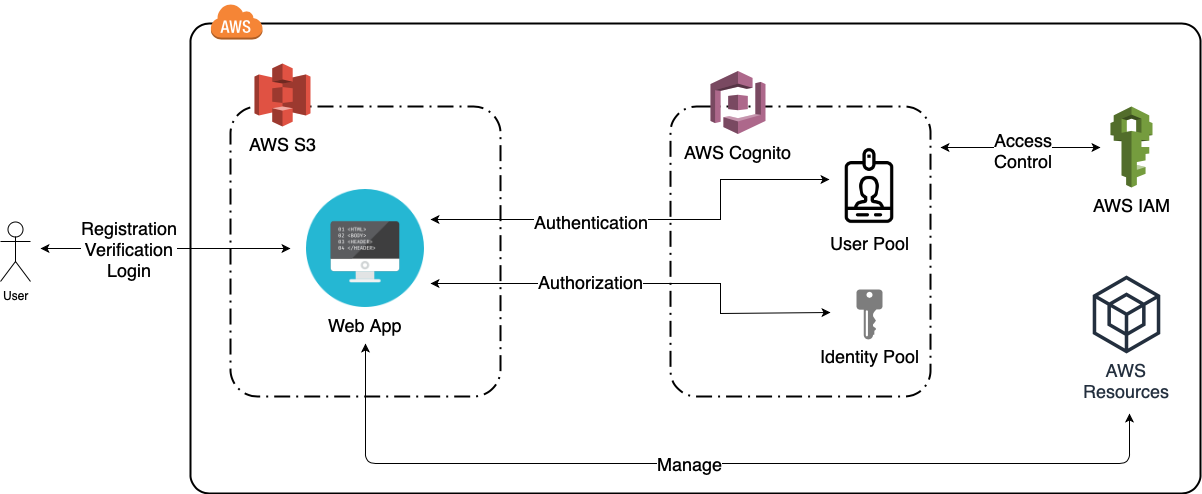
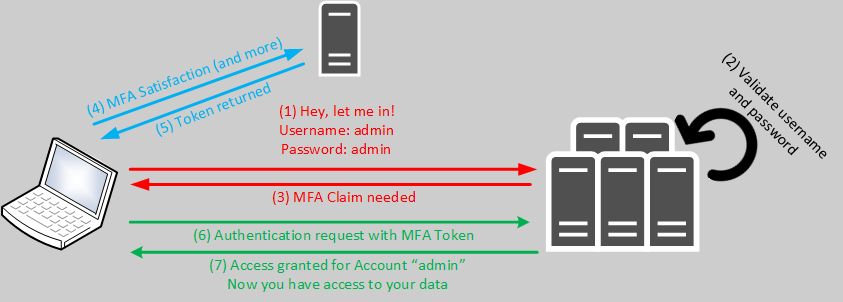
Building An Integration Framework for AWS Cognito Login and Authentication - TrackIt - Cloud Consulting & S/W Development

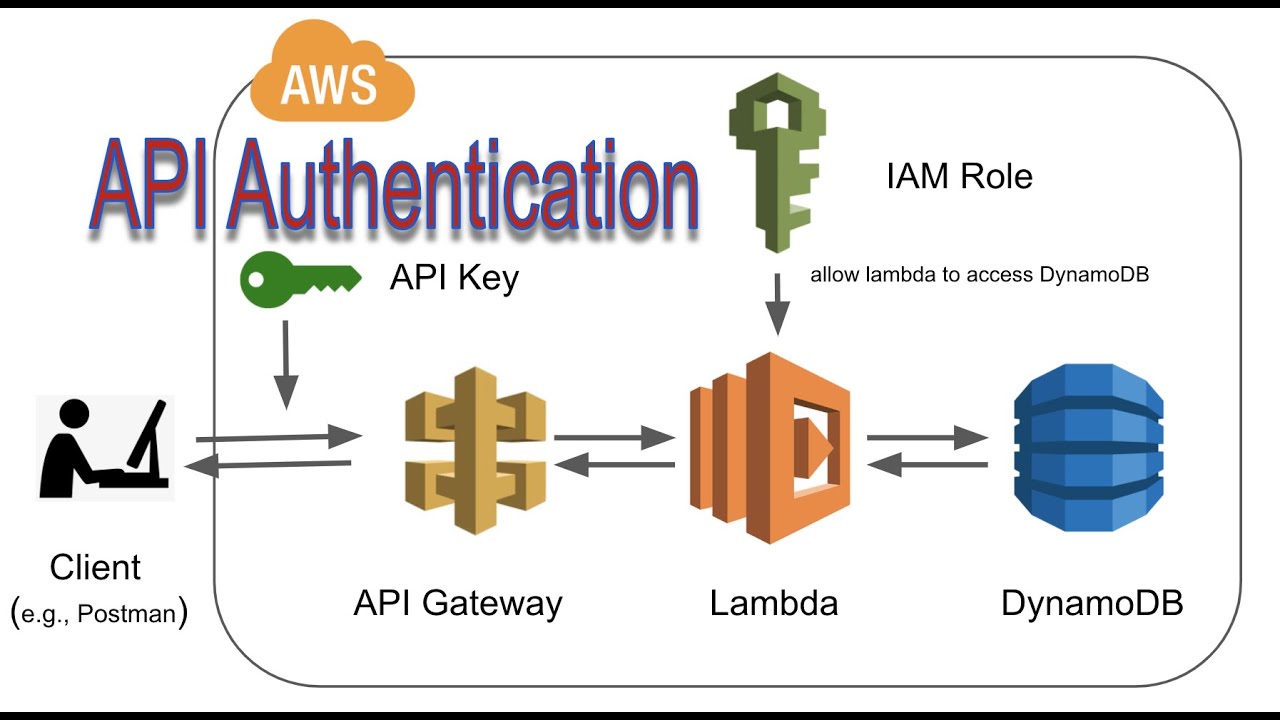
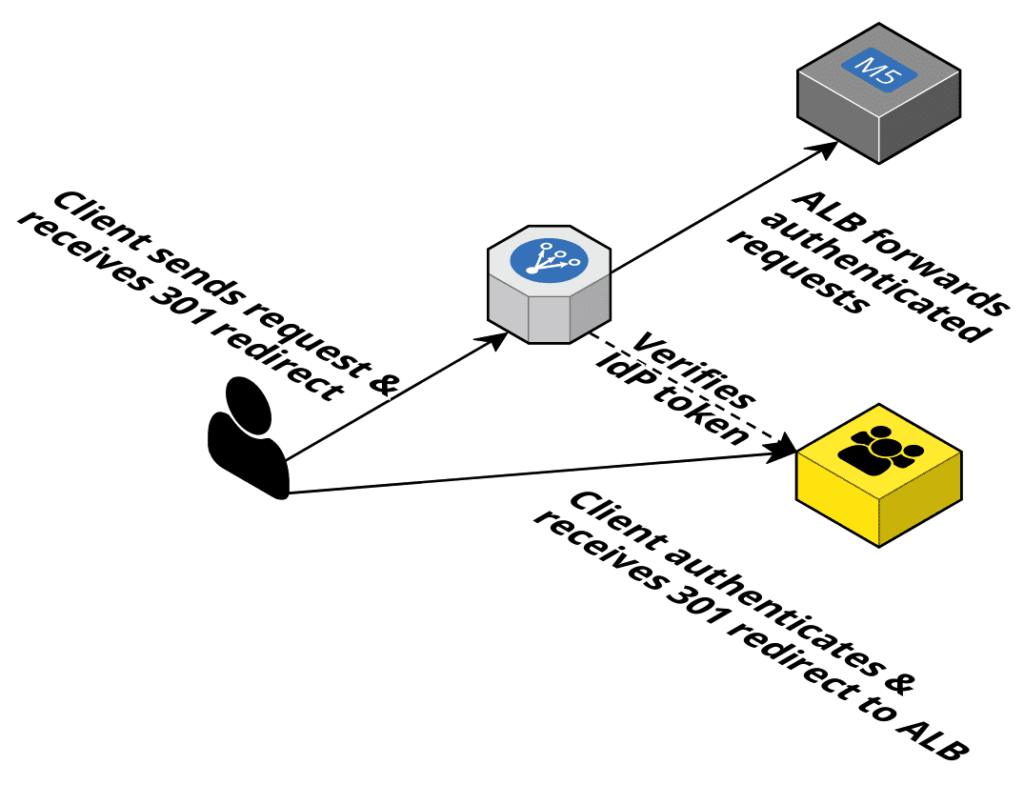
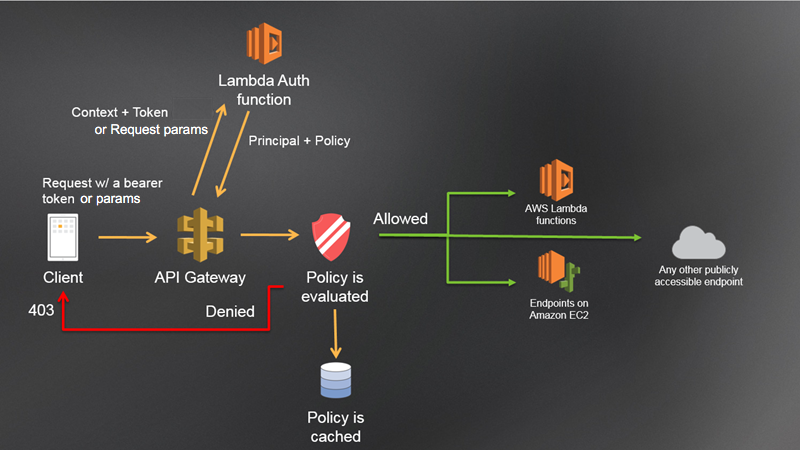
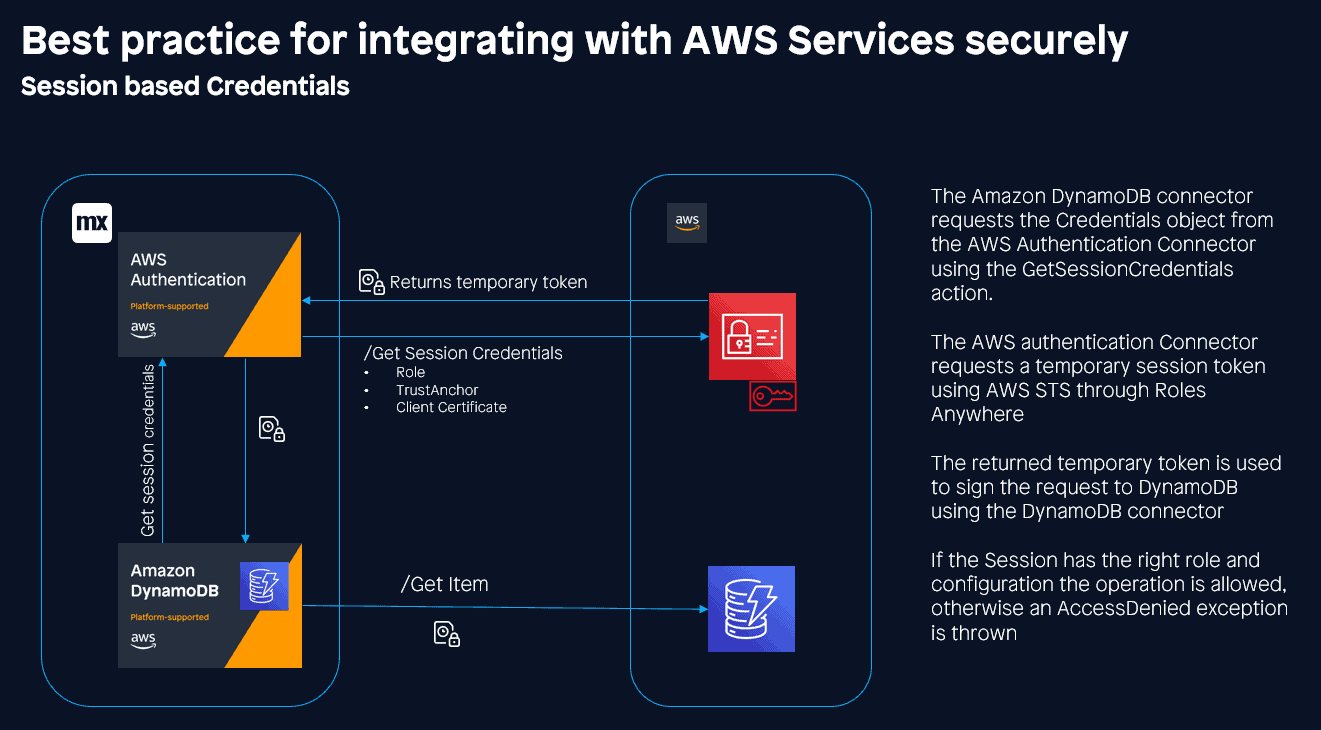
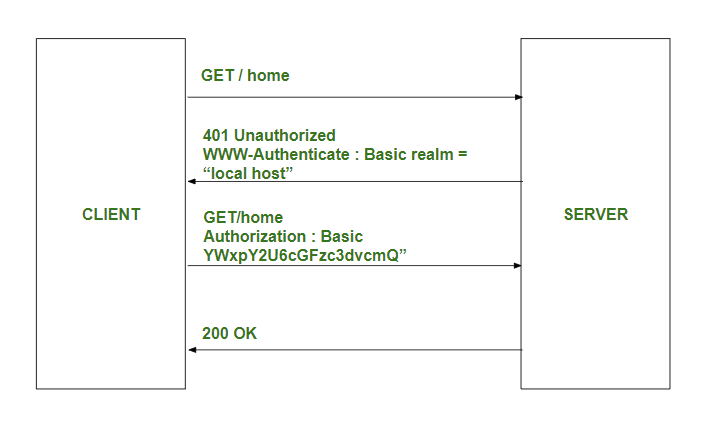
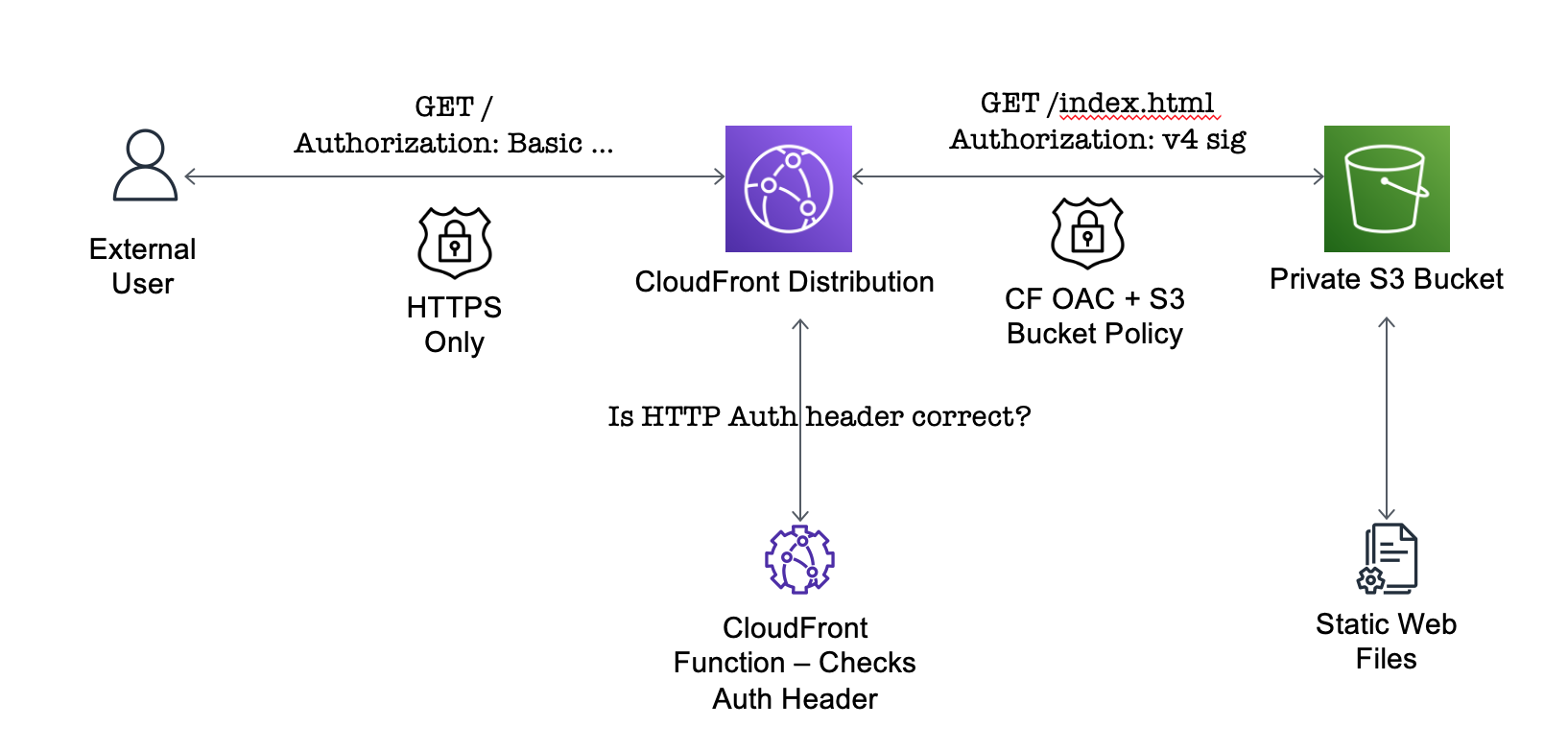
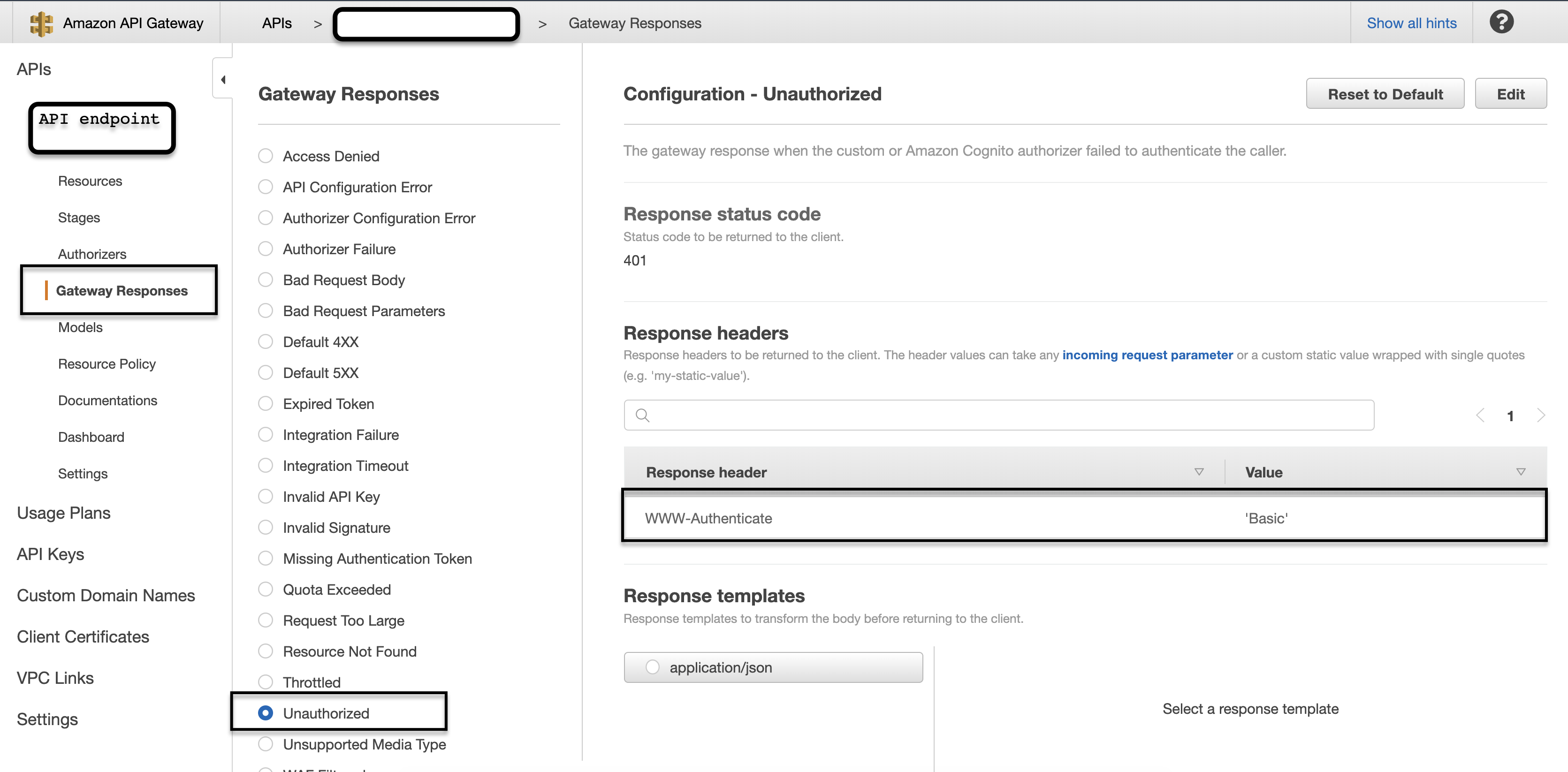
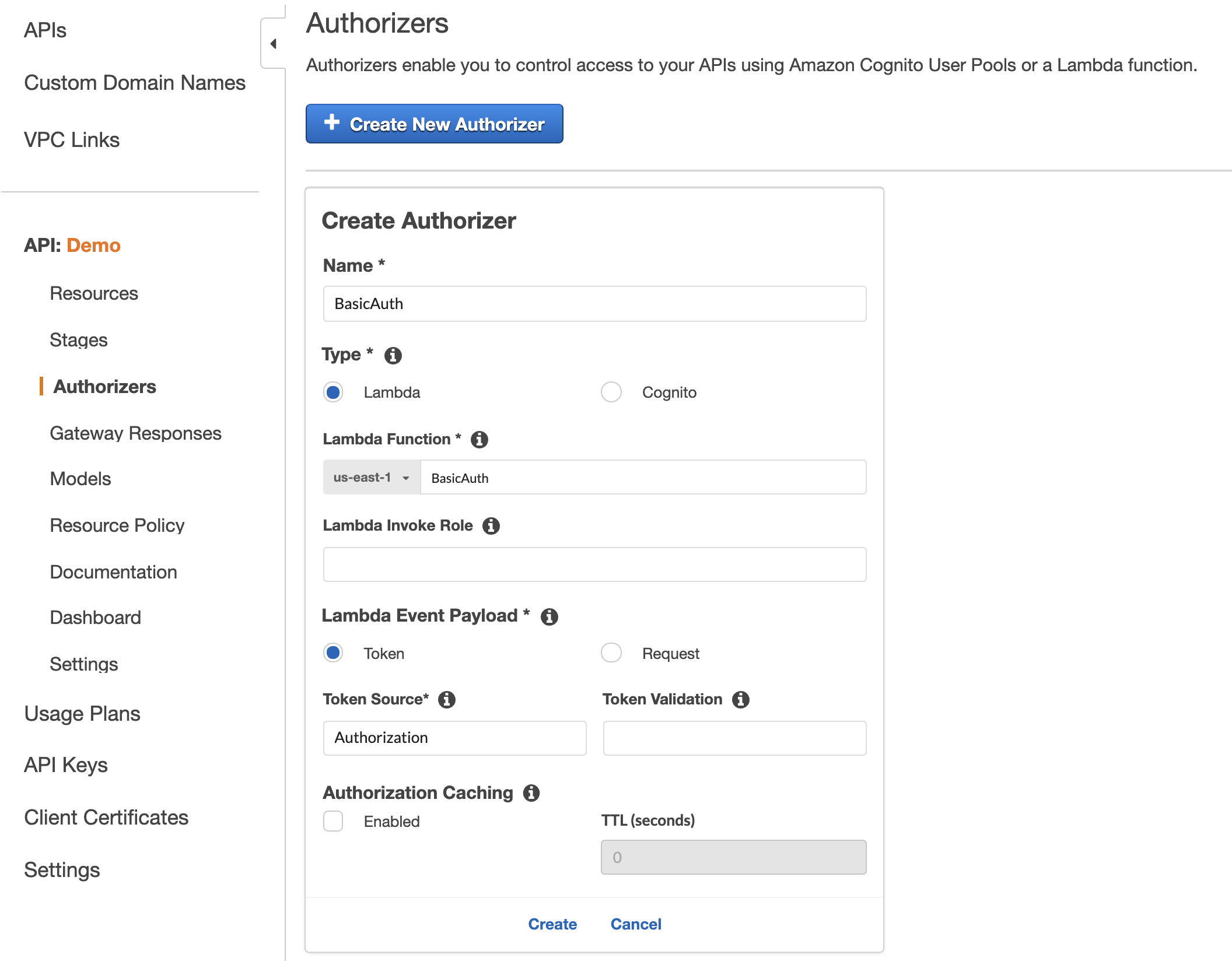
Approaches for authenticating external applications in a machine-to-machine scenario | AWS Security Blog

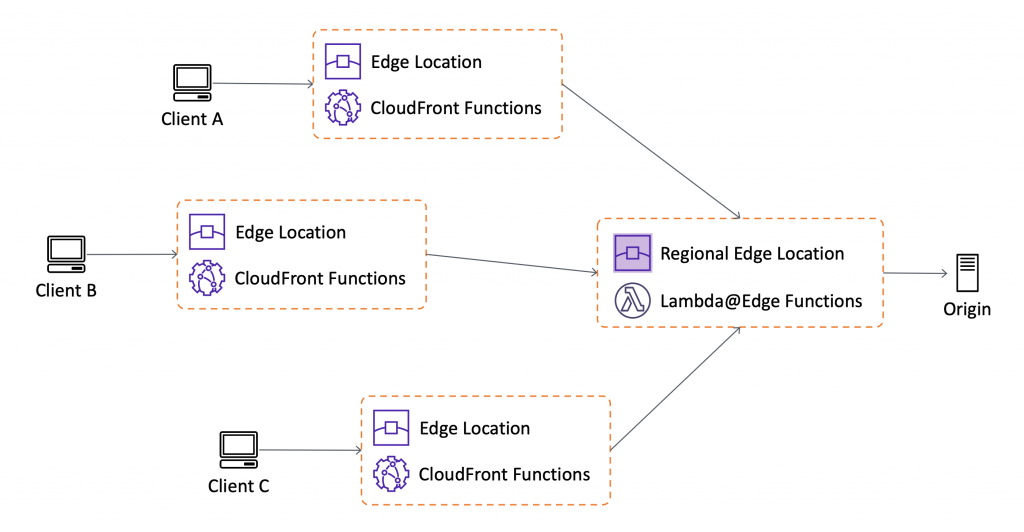
AWS Web Identity Token Authentication in Legacy Applications | by Jonathan Merlevede | datamindedbe | Medium